The new administration has the chance to fix what Trump broke about the internet.
Read MoreTargeted Security
Using the latest trends, models,
and research to bring
network security to the user.
Scroll down to learn about our
Home Cyber-Defense Initiative.
Available now!
Executive Brief

Mission: Monitor Home Networks for attacks and malware, and consult with users for remediation in order to prevent personal data from being compromised and prevent home devices from being used in bot-attacks on business and government agencies.
Priority: High
Justification: Home routers and devices, especially IoT devices, are notoriously vulnerable and rarely have security patches applied.
Summary Points:
- CyderInc provides cyber-security using a Network Intrusion Detection Sensor (NIDS) digital device.
- The NDIS may be a netbook or SoC devices, and remains owned by CyderInc.
- The NIDS is monitored and maintained remotely by CyderInc, requiring sparse input after setup.
- The NIDS alerts the user and CyderInc in the event of a network intrusion or malware spreading.
- CyderInc assists in removing the virus/malware if needed.
- The NIDS assists in increasing home network security.
Value:
- Help prevent identity theft, asset theft, and monetary loss from cyber attacks.
- Offboarding of network security analysis, saving time.
- Personal consultation for specialized application of security.
- Protect other users and their data on the home network.
Conclusion:
Users concerned with identity theft, password loss, online banking interception, and/or monetary loss from cyber attacks can benefit from this service. The Network Intrusion Detection System is supplied by CyderInc. The NIDS listens for incoming attacks, then alerts CyderInc and the User. CyderInc then assists the user in remediating the threat, by helping remove the virus that has already established on their devices, and assisting the user in preventing further attacks. This system is perfect for users of a high net worth, users who don't have the means or technical ability to defend themselves from cyber attacks, or users who have jobs that make them the target of cyber attacks.
Recommended Action:
Click the link below to learn more and subscribe to the service.
Purchase a monthly subscription with Holiday discount
Purchase a discounted Subscription to cyderinc's home cyber-defense initiative: normally $150/month
CYDERINC'S Home Cyber-Defense Initiative

When you subscribe to CyDeRinc's Home Cyber Defense Initiative, you will receive a small device that has been custom configured to listen for attacks and probes by bots, hackers, viruses and malware. Plug it into power and your internet, and it's ready to go. This device has a small screen that shows you its status, your internet connection status, IP addresses, and the last time it was probed/attacked. Also included in the information is the IP address of where the attack came from, which allows you to know if the attack is from malware on one of your connected devices, or if an attack made it through your router.
The attack information is sent to CyDeRinc, and one of the cyber security consultants will quickly alert you by text, call, or email. The consultant will then assist you in removing the malware, if it came from a device on your network, or in toughening the defenses of your router, if possible, to prevent another incursion.
Also, when you subscribe, CyDeRinc will monitor the function of the intrusion detector and work quickly to make sure it is working at its optimum capabilities. Of course, tech support for the device is also included with the subscription, should you need it. But with its self monitoring capabilities and reporting in to the CyderCloud (TM), we verify it is working correctly.
Scroll one more page, or click here, to read about how our service and NIDS device work together to protect your network and personal data.
These days, it's not good enough for only corporate networks to have cyber defense experts looking out for them. Home networks are highly vulnerable and can be used in attacking other corporate or government networks, not just stealing your account credentials. Whether you ask us to assist you or not, scroll down to our PERSONAL CYBER SECURITY
page to read about steps that you can take to help secure your digital life.
Click here to subscribe but scroll down to read details first:
https://www.cyderinc.net/#section-62b0fde043508
Click here for more information:
https://www.cyderinc.net/in-the-digital-trenches/how-cyderinc-s-home-cyber-defense-initiative-works
Current device Used by CyDeRinc to monitor networks:
https://www.armbian.com/orange-pi-prime/
Think you don't need to monitor your network?
Windows Devices:
https://tech.co/news/raspberry-robin-worm-windows
https://www.msn.com/en-us/news/technology/microsoft-warns-about-android-malware-that-could-secretly-steal-your-money/ar-AAZd5dP
Home Routers:
https://www.techtarget.com/searchsecurity/news/252510453/Hundreds-of-new-vulnerabilities-found-in-SOHO-routers
https://www.infosecurity-magazine.com/news/80-of-soho-routers-contain-vulnerabilities/
https://www.ise.io/casestudies/exploiting-soho-routers/
Android:
https://www.tomsguide.com/news/malware-infected-apps-hit-over-3-million-android-devices-delete-these-now
https://www.laptopmag.com/news/malware-infested-android-apps-were-caught-stealing-money-do-you-have-them-on-your-phone
Apple Products:
https://www.cnn.com/2021/02/21/tech/mac-mysterious-malware/index.html
https://www.cnbc.com/2021/05/19/apples-head-of-software-says-current-level-of-mac-malware-is-not-acceptable.html
https://www.the-sun.com/tech/5758291/warning-millions-iphone-malware/
*not affiliated with Orange Pi, Armbian, CNN, Apple, Microsoft or info links above, all of whom retain their trademark rights.
home cyber-defense initiative details
Personal cyber security

First, passwords. Every little site requires a user name and password so that it can track you and monetize your online viewing. The important ones, like banks, stocks and retirement accounts need special attention also. So how do we remember all these bloody passwords? At home, it's fine to write on a piece of paper to keep in your desk. That shifts the threat to one of a physical presence and if someone has access to that paper, they've either broken and entered your house already, or betrayed your trust. This shifts the security of the list to the local physical realm from the world-wide digital.
A password manager can also be used. They are available for Windows, Android and Apple products, but bring their own risks. A cloud based password manager, while convenient, puts the security of all your accounts on the cloud/app provider. Frankly, they won't be held accountable when they get breached and all their users accounts and passwords are sold on the dark web.
A password manager that isn't cloud based and doesn't auto update itself is more secure, since
the data remains local. Turning off auto-update means malware can't sneak into an update but also means that you miss any updates that patch vulnerabilities. And everything has vulnerabilities.
In Windows, you can keep a Notepad/Wordpad file on your desktop, listing your username and passwords. You can also create a folder with a .txt file in it for each account. Either way, right click on the folder or file, choose properties, then click advanced, then click Encrypt contents to secure data. It may ask if you want to encrypt the file or folder and tell you that encrypting the whole drive would be better, but go ahead and stick with the file/folder for now. A popup notification should ask you if you want to export the key. You need the key. If the system can't find the key, your data in that file will be unrecoverable. So click to save the key and export it to a folder other than Documents, or better yet, export it to a usb drive you store in your safe or in your desk.
Encrypting the file this way in Windows uses the Windows Bitlocker drive encryption to protect the data. There are other services not attached to the Windows kernel that you can download, and encrypt the file. These offer another level of protection but every method has its own vulnerabilities. Security is always a convenience versus security balancing act.
On the mac, there are apps in the store that can encrypt files, as well as password managers. Follow the same criteria for choosing these.
However you record the passwords, there is no need to record the entire thing. If a password is '1922 graceful pluto destruction 2022', then pick a part of it to stay the same for every website, then don't write that part on your record. So, you know that the thridword is always pluto, then uses x's for it instead when you write it down. So in the file or on your paper it would read '1922 graceful xxx destruction 2022'. Thus even if the file is compromised, it is not a complete password. You know that xxx means 'pluto'. Also, pick something related to the website also to vary your password. If the website is homebuilders.net, you can add an HBN somewhere in the password and use XXX to symbolize it on your list.
Browsers on most platforms ask you if you want to store login information when you use it. This is the least secure way to store the password as your browser is vulnerable to nefarious servers. Only use this for the least valuable, not asset linked, accounts.
Second, links. Never enter your login data after following a link via email or text. Website login pages are easily copied and moved to servers where they can collect your data then forward you to the real site for you to enter it again. You'll just think you hit a wrong key, when in fact, you just gave your login and password away. This type of credential stealing is call phishing and it happens via email and text. Never follow the links to enter your credentials, unless you were expecting it. Executive and high value persons are often targets of specific and personal cyber attacks like this. Spear-phishing executives is very common and with a broad enough campaign, is almost certain to be successful against the person.
Third, be wary of the apps you put on your devices. Make sure they have a good reputation. On computers, you can visit virustotal.com and submit the download and they'll check it for malware and reputation. Be careful, malware is always being snuck into Google's Play Store and Apple's App Store.
Fourth, don't use common user names for any of your accounts if you have a choice. User names like user1, admin, default, and thousands more are used by bots to brute force their way into accounts. If they get your username, they only need to brute force your password. If your password is weak, it won't take long for a compromised server to brute force your account.
Fifth, use strong passwords. The old way of changing passwords every 90 days and using a number and character has been proven to be easily compromised. Changing passwords means users will create weak passwords they can remember. It also means malware can compromise the password reset server, or just intercept traffic (neither particularly easy) since they know all users have to reset the passwords every so often. However, making passwords expire by the calendar makes the users very susceptible to phishing attacks titled "Time to reset your password". Since the user is expecting it, they won't be wary about putting in their credentials to the hacker's server. They think they're doing the normal password change. IT'S BAD POLICY TO REQUIRE PASSWORD CHANGES FOR UNCOMPROMISED USERS AND HAS BEEN ACCEPTED AS SUCH BY NIST FOR YEARS.
So how should passwords be chosen? The new password standard, since around 2018, has been to choose unrelated words that form a long phrase. Use a series of words that don't make sense together but you can remember (or put in your encrypted file). Websites that only allow 8-14 characters are way behind on their security so take note if this happens with your accounts. So choose 3 or 4 unrelated words to string together in a phrase, and change them slightly for every web account. Never use the same password for all your accounts.
Sixth, don't link your accounts. Don't use your Google or Facebook account to log into third party sites, even though it is more convenient. Many people have been lax in doing this and have had all their accounts compromised in a single cyber security incident. Use different users and passwords for each account as is possible. Don't use the same account to log into multiple sites. Just don't.
Seventh, two factor authorization is better, but not as good as claimed. Text messages for login are easily intercepted or copied. Emails are slightly better, depending on the provider. Two factor authorization can help against broad cyber attacks by bots, but if a hacker is targeting you personally, you'll find there's very little that will protect you. We all make mistakes, and attacks come in broad swipes. It only takes one mistake and they can try thousands of times with their servers.
Eighth, protect your home network. Keep each of your device's anti-virus up to date and be careful of the software installed. Our Network Intrusion Detection System is a good way to know if one of your devices has been compromised or if someone is attacking your network specifically. Similarly, you have to secure your modem and router correctly. If you're using rented modem/router and it has the default username and password, then your home network is wide open to attack. So change the usernames & passwords on the router login, and set the firewall to secure settings. Check and see if there's a router update for yours, since they occasionally patch for performance and security issues. These patches, however, are very rare and routers have many security holes that are never patched, leaving your home devices vulnerable as well.
For these reasons we recommend not renting modems and routers, but buying your own. Not only will you save money, but you can configure them appropriately to help protect your digital home life. With networked cameras becoming popular, this is even more critical. CyderInc started by helping users with this process. Check back for articles and how-to's.
Last, remember, Cyber-Security is a mindset, much like physical security. There's no silver bullet. There is always someone or something attempting to get into your home network and each of your devices. Thousands of server bots descend on a vulnerability when one is discovered. Last time we watched a purposefully vulnerable device ( a honeypot), there were more than 4 thousand attacks in an 8 hour period. The bot swarms not only try to break into your devices, they steal the bandwidth you pay for. Subscribe to our Network Intrusion Detection Service and let us help protect your digital life.
High Value Persons & Families:
Certain persons who have worked hard their entire life and have reaped the benefits of their hard work are vulnerable to attacks on them specifically. We call these users HVT's, or High Value Targets. Even your job may make you an HVT, and cause hackers to aim at you specifically with digital attacks, spear-phishing particularly. Corporations with officer's names listed on websites make those officers targets. Even public business filings provide enough information for a digital attacker to hone in on you specifically. Let CyderInc help protect you. If you have already experienced some of this, contact us immediately, and put our experience to work for you today.
The cyderinc nids for enterprise networks

Your enterprise also could have data stores that don't face outward and aren't facing constant attempts to login and exfiltrate vast amounts of data. You should be using a log aggregator here as well. If you're not, then our NIDS is right for you. It can tell you what was attempted and from which IP. As a honeypot that replicates many different types of servers, it also can keep hackers busy as they fruitlessly attempt to break into what is not really a server.
Our NIDS can be fully customized to meet your needs. We will sell it to you for a flat fee, provide a year of support, and let you run it, manage it and make sure it's functioning properly. But in case you don't need ANOTHER device to monitor, we can monitor it for you.
The CyderInc NIDS only sends data to CyderInc that pertains to the device itself. It does not sniff other network traffic. It does not monitor other network functionality besides itself. Every two hours and at boot, it sends a status file to the CyderCloud that contains function checks, IP addresses, private key information, and uptime. You can even monitor the device using the html server run by the device. It is a python3 server, serving html that requires authentication to view. So it's not likely a bot or malware is going to find true vulnerabilities in its service. But, if the device is compromised, which would be picked up by one of the many security checks, you would know there is probably a live hacker on the other end attempting to do damage. We'll monitor the honeypot and let you know when an incursion occurs, from what IP it came, and what vulnerability they attempted to use to gain access. If a hacker has already compromised a server and is attempting a lateral move, the NIDS records the IP from which the attack came. Since this system has only been in beta testing for the last year, it's unlikely they'd recognize what they're dealing with, though they'd certainly come to the honeypot conclusion when they kept getting stopped.
Monitored or unmonitored, we can help you secure your enterprise network. The CyderInc NIDS is a valued indicator of compromise on today's digital minefield. Call or email and we'll happily configure our CyderInc NIDS for your wants and needs.
Truth about vpns: a non-technical analysis

All the traffic coming from your home network, from behind your router, shares the external IP of your router. The internet side (WAN) gets an IP address like 72.43.124.56 (which we'll use for our examples) and the home network side gets an address of 10.0.0.1 or 192.168.0.1 ( or a derivative as defined by standards). So all traffic from behind your router, on the LAN, uses the return address of 72.43.124.56. A service on your router called NAT keeps track of which traffic is coming from which device so it knows where to send return traffic. So my pc has a LAN address of 192.168.0.34, which my router assigned it using the DHCP service. But, when I type in www.newegg.com in my browser, something else has to happen first, it has to know the IP address of newegg.com, which is different based on your geographical region.
Typing https://www.newegg.com in my browser causes my computer to check it's recent memory and see if I've accessed newegg recently. If so, it gets the newegg.com IP address from memory. If not, it goes to the router, who see's it sending a DNS request, and sends the request to a DNS server, as set in the router, to get the correct IP address of newegg.com for my geographical region. The DNS server sends the correct IP address back to the router at 72.43.124.56. The router keeps track of connections and sends the DNS request back to 192.168.0.34.
Next the computer uses the IP address of newegg to make an https request to https://www.newegg.com . The newegg server establishes a connection to the router which passes it through to the PC. The newegg server asks for the type of device requesting the web page (mobile or desktop) and for the type of browser being used. Using this information, the server sends the correct web page back to the browser and shows you a correct page for your geographical location, your browser, and your device (mobile or desktop). All this happens in milliseconds with a good internet connection.
But in this interaction, you have revealed information to both the DNS server and the newegg server. You have revealed your geographical location, not down to the street level, but usually the closest city. You have revealed to the DNS server that you're visiting the newegg.com site. All this comes from the 72.43.124.56 address.
Servers use the geographical information to offer their services only where they are allowed. Parts of Xfinity's DVR services are only available if you connect from your home IP. Many streaming services have to limit their programs by country as well. Using your IP address is how they do this.
So now what does a VPN actually do? I provides you with a fake IP in another region. If you're traveling in Europe, but want to view programming in the States, you use a VPN to say you're in a particular city. Usually there are many cities and countries to choose from with good VPN providers, so sometimes you get to choose not just the country you want to pretend to be in, but the city in that country.
Now not only does a VPN provide a different geolocation, but it provides a light level of anonymization. Each VPN connection shares an IP with other users of the VPN, so it makes it harder to actually trace the traffic back to the real original IP. Lots of users using a single VPN address is a light level of protection against tracing who was making the connection.
Some VPN providers also provide a type of DNS protection that protects the user from the DNS server knowing who actually made the request for the IP address.
So a VPN provides a low level of anonymizing and DNS protection. Why would we care? Your ISP uses this data and sells it, just like Google sells what it learns about you from google.com and your Android phone. A VPN does help you from being taken advantage of by the services you are already paying for.
Again, a VPN tunnels your data from your device to the VPN server in the country/city you choose. Then from there the internet works as normal.
But, for a VPN to work, it has to keep records of what data is going where. Some VPNs say they don't keep paper or digital records, but there is no actual way to verify this until they get a warrant from a government demanding to know about a specific connection.
Similarly, the way the internet and server work, if there's not a record on the server ( at least temporarily), your data won't get back to you. Also you have to consider your billing and payment method. If you pay by credit card, then there is certainly a record of you buying the service.
The way servers work, if there isn't a record of connections to where and the speeds, then there can't be any type of service improvement or Quality of Service, as it's called on an internet adapter. Some VPNs block downloading torrents from sites like Pirate Bay. So unless they're monitoring your connections, they wouldn't know if you were torrenting. So some level of records are required for a VPN service to function.
So is it worthwhile? It depends on what your threat-vector is. Are you concerned with government accessing your browsing behaviors, or are you concerned with hackers and google stealing your browsing data to sell it without your approval? VPNs are more effective against non-governmental spies.
To provide another level of obfuscation, if you are concerned about federal spying on your browsing and transactions, you should use a VPN not headquartered in the United States or Europe ( or in your country). Not that it makes it impossible, but it just adds one more jurisdictional level of hassles for spies to go through to monitor your browsing data.
For countries where websites are restricted, news only comes from the government, and websites need approval by censors, a good VPN will bypass the restrictions by making it look like you're in another country. But again, this requires caution in picking a secure VPN.
For years, the United States government bugged cryptographic hardware sold by the world's biggest cryptography company. How do you know the VPNs aren't secretly run by governments? Judging by history, I guarantee some of them are. Which ones? Good question.
Another issue with VPNs is that since the internet moved to https (encrypted connection webservers), it's more difficult for third parties to see what data is being transferred. The IPs aren't hidden, since the routers and switches need to know where the data is going and coming from, but the data enclosed in the packets is encrypted. Again, it's not impossible for someone to perform an attack and steal the certificate for the packets, but it is much more difficult than it use to be with http. Https decryption keys are different for each connection ( conversation per device) so it does provide a decent level of protection again low level hackers and generic threats. Pushing https is one of the good things Google has done for the network. Before that, it was much easier to read the network data and even pretend to be a server in order to steal passwords and funds.
A good VPN will provide a certain level of protection for emails, geolocation, downloading a pirated movie or two, or downloading pirated software. If your computer uses IPv6, you'd have to get a VPN that protects IPv6 as well as IPv4, or you won't be protected. While on a VPN, it's just safer to disable IPv6 on your device.
The highest level of security is provided by the TOR network. TOR was developed by the United States Navy to enable secure communications, but every few years another vulnerability is found and exploited in that as well. TOR is also slow, because of its routing methodology which is how it provides the anonymity. There can be nefarious TOR bridges (as their called) or nefarious exit nodes on TOR also. But for all the technology available to non military civilians, TOR is certainly the most secure. But with the constant balancing between security vs. convenience, TOR is usually only used in the most critical situations.
So while we shouldn't believe all the advertising about VPNs, they have their place and proper use. ( Some apps even use geolocating as a security measure as well, like a banking app not letting someone from Pakistan log into your bank account in California ). Do you need one from email or online purchases? No. For browsing the latest bowel reconstruction techniques? Not really, unless that's illegal in your country. For downloading a copy of that movie you have on VHS so you can watch it without a VHS player? Sure. For downloading a preactivated copy of Windows 11? If you want malware in your Windows, sure.
IN THE dIGITAL TRENCHES...
After two years of development and 6 months of remote testing, CyDeRinc's Home Cyber-Defense Initiative is now available!
Read MoreThe Tricks to installing Pihole on Linux Mint and routing a TP-link Archer A9 to use it.
Read MoreSenators Try to Side Step 4th Amendment Due Process Once Again.
Read MoreWhy You Need Personal Network Security.
Read MoreEnterprise Network Defense is Available!
Read MoreDigital Privacy Blog
The push to work from home in order to slow the spread of Covid-19 represents a major avenue of attack for Cyber Criminals.
Read MoreThe Incomprehensible Idiocy of the LAED Act.
Read MoreA.G. Barr attempts an end-run around the Bill of Rights while the world is focusing on Covid.
Read Morehttps://www.schneier.com/essays/archives/2014/01/how_the_nsa_threaten.html
Read MoreA.G. Barr's July speech was revealing, not just about what he thinks about the Bill of Rights, but what he thinks the future should be.
Read MoreAny technical person can find a handful of illogical assertions in A.G. Barr's speech. Here is a link to a Cyber-Security heavyweight's thoughts on one of those logical flaws.
Read MoreTrump's AG Barr is pushing for 24/7 access to everybody's phones and threatening to outlaw Apple for using strong encryption.
Read MoreArticles, Rants & Raves

AnyDesk follows TeamViewer by Turning Against Users
AnyDesk has recently started notifying users that using the software too often means it's being used for business, and that's not allowed. Just like TeamViewer did, they're now making you wait so many seconds before using the software.
Learn More
Blocking Advertising Streams and Malacious Links on Web Pages
Pi-hole is a Linux program created to filter listed sites from webpages. Functioning as a DNS server, it reduces network load and adds to security infrastructure.
Learn More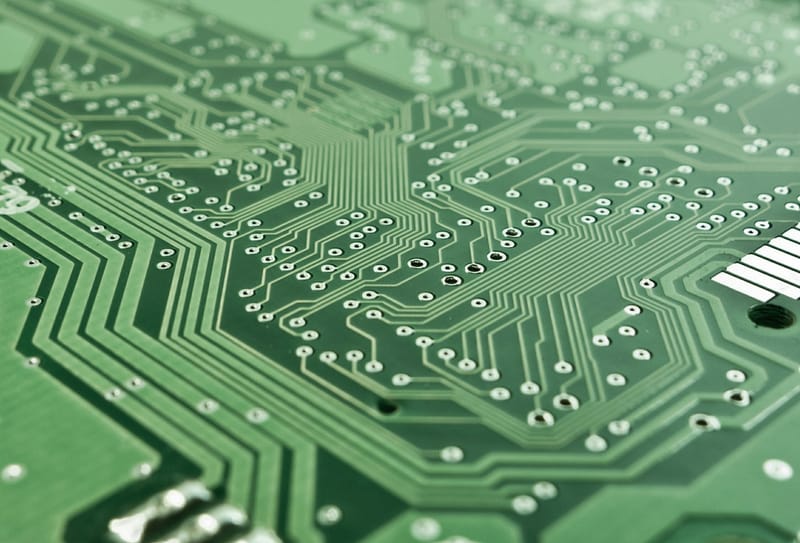
Windows 2004 Setup
Windows version 2004 is another step toward Desktop as a Service. While this is fine for users with always available high speed internet access, it still causes privacy and security issues for personal users.
Learn More
On The Ending Support of Windows 7
Beyond the doomsayers, what does ending support for Windows 7 really mean?
Learn More
Mobile App Security
When an app asks for far-reaching permissions while being installed, you know they're up to no good.
Learn More
Traveling With a Smart Phone
What to do, what not to do, and where... (regarding your phone of course!)
Learn More
Archive: VMWare Workstation 15 in Windows 1903x64
Windows 1903 makes significant changes to Windows. This causes significant headaches to anyone using VMWare & other programs (Macrium Reflect & other backup programs) as well. Also read on to learn how to block Windows updates.
Learn MoreExecutive & Personal Cyber-Protection Program

Your Cyber-Defense
Our duty is to protect Affluent People, Executives, and their Families from constantly evolving cyber threats. Using threat analysis methodology and real-time analysis, we provide a robust & comprehensive cyber defense.
Learn More
Are you using Siri, Google or other voice assisted technology?
If you are, then you have no legal right to digital privacy. Since what the device picks up has to be processed to know if you're saying the key word, IT HAS TO BE LISTENING IN ORDER FOR IT TO WORK. What your device hears is not protected under legal privacy rights if your device sends the information to the Apple or Google server. And they send what they hear to their AI servers to improve the service and for the quality technicians to review. If you're using one of these services, you have legally given up your right to privacy wherever the device is located. Supreme Court has ruled that any data on a server you don't own (the cloud or internet) has had the right to privacy waived. Since it sends an unknown and variable percent of what it hears to the cloud, you're giving up your legal right to privacy on all that gets sent. EVERYTHING YOUR DEVICE "HEARS" CAN BE CONSIDERED PUBLIC INFORMATION.
server administration: ins and outs
Contact Cyder inc.
Map
about

Visit our Facebook page Cyber Defense & Research Inc.
Cyber Defense and Research Inc is not affiliated with any companies mentioned in any of the articles or blogs. The trademarks belong to the companies.